Secrets in code combined with code leaks exposed data for 300,000 Toyota customers

There has been a surge in the number of organizations who have reported theft of source code, exposure of secrets in code as well as exposure of proprietary code into external repositories due to unauthorized access or code leaks. This is exactly what happened at Toyota. It was reported in an article dated October 10, […]
Integrating code security with CI/CD and enterprise tools
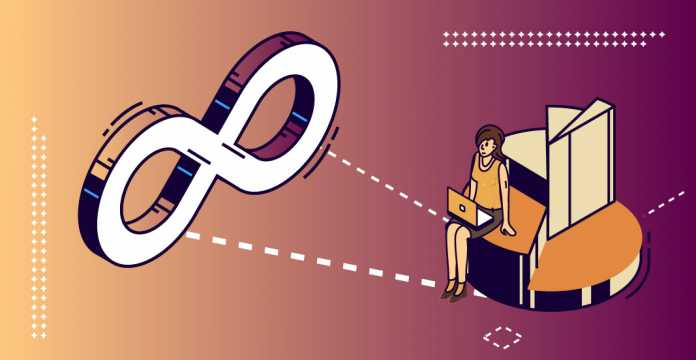
Developer teams work hard to deliver high quality code that meets business requirements. Having an internal development team that produces source code is a huge investment for any size enterprise. Optimizing these investments creates the drive to deliver more code faster, with higher code quality and that is written to be secure as well. End-to-end […]
Integrating code security tools with developer workflows
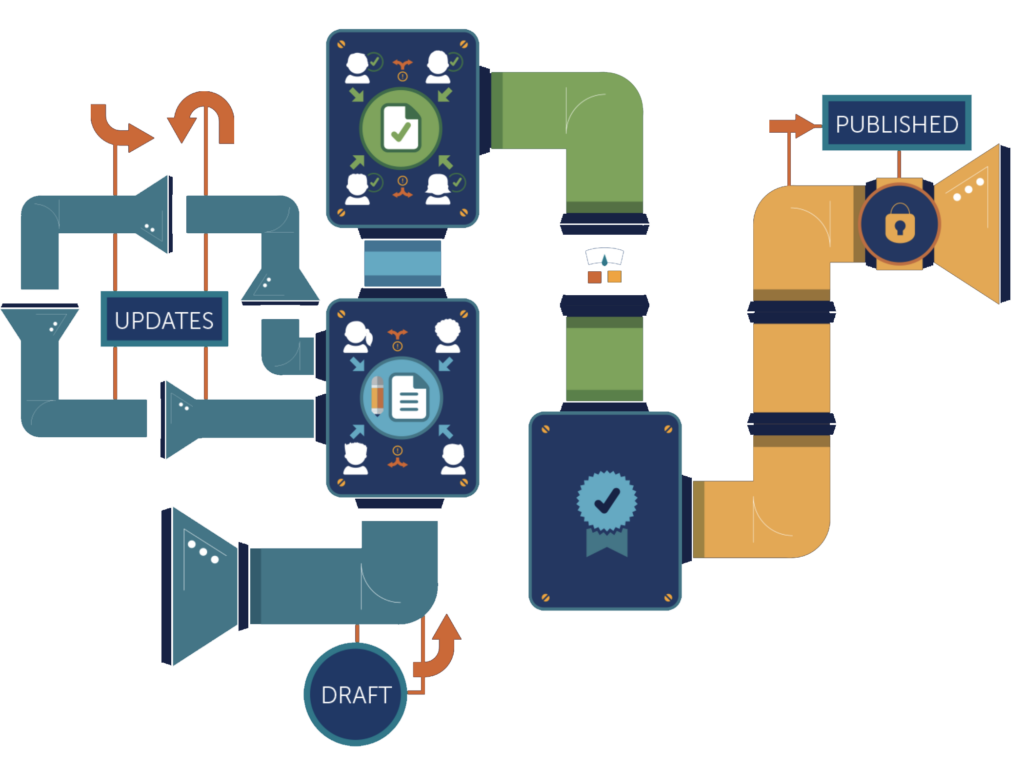
Based on a survey of 350 developers, IT and application security teams, developers are working to incorporate security into development, they face multiple challenges keeping up with the speed and volume of releases with CI/CD. The most commonly cited are software being released without going through security checks or testing (45%) and the lack of […]
Blog: How BluBracket identifies risks in source code to enhance code security

There has been a surge in the number of organizations who have reported theft of source code, exposure of secrets in code and in many cases, their proprietary code getting exposed in external repositories due to unauthorized access or code leaks. In a recent survey we conducted with ESG that included 350 IT, application security […]
BlakHat Innovation Theatre – Most overlooked gaps in the software supply chain

The Software supply chain has taken center stage in the fight against cyber attacks and breaches. Savvy threat actors are leveraging gaps in the software supply chain to mount an unprecedented number of attacks. Organizations developing software are adopting automated DevOps and CI/CD pipeline solutions to speed up the development and testing all the way […]
How to protect your Google Cloud Platform (GCP) secrets

Google Cloud Platform (GCP) may be the smallest major cloud, but it’s one of the fastest growing thanks to its close association with Kubernetes and the company’s liberal habit of giving startups free usage credits. GCP’s default configuration and policies offer substantial security for applications running on GCP infrastructure, but none of that matters if […]
How unauthorized access to Git became a big headache for Twitter

You would think organizations would want to know when ex-employees have access to the crown jewels. No one wants to end up in the news like Twitter did due to lack of access controls for repositories that contain source code just as they are locked in a battle of wits and a highly publicized lawsuit […]
Gartner recognizes BluBracket in two Hype Cycle Research Reports

In its latest reports Hype Cycle for Application Security and in the Hype Cycle for Agile and DevOps, 2022, Gartner recognized BluBracket as a vendor in the emerging segment of Securing Developer Environments. What Is the Gartner Hype Cycle? According to Gartner, the hype cycle depicts a common pattern that occurs when an innovation emerges. […]
SiliconANGLE includes BluBracket in the top cybersecurity innovator list at BlackHat 2022

SiliconANGLE published a list of the Top 7 cybersecurity innovators from the myriad of companies that exhibited at BlackHat 2022 in Las Vegas, August 6-11, 2022. As part of the vetting process, BluBracket conducted a briefing with Jason Bloomberg, founder and president of analyst firm Intellyx, which advises business leaders and technology vendors on their […]
The World’s Largest Breach. Root cause: Secrets in Code

On July 3rd, Changpeng Zhao, the highly regarded CEO of cryptocurrency exchange Binance, posted a tweet under his widely known moniker CZ, alerting the world to a massive data breach that in part read, “our threat intelligence detected 1 billion resident records for sell in the dark web, including name, address, national id, mobile, police […]