We are in the midst of many generations who have grown up building things with Lego blocks.
Guess what! software is being snapped together in part pieces as well. You don’t have to write every last bit of code yourself. You can also mix your code with open source code and deliver finished applications much faster. Organizations developing software are adopting automated DevOps and CI/CD pipeline solutions to speed up the development and testing all the way to deployment.
Developers and their managers are ecstatic about the increased productivity and being able to deliver more in a shorter period of time. However, security experts agree that the software supply chain and code vulnerabilities have become the most critical aspects contributing to enterprise risk.
A common problem for DevOps teams is that adding security into the mix introduces too much friction into the development process. Many developers have admin-level access for infrastructure and often find ways to bypass security. Not because they are malicious, but because they want to get their code working perfectly. They have every intention of coming back to fix issues related to security once it’s all working perfectly. The reality is that rarely happens and application security ends up taking a back seat to speedy deployment.
Developers, AppSec and IT Ops teams absent of a unified application security strategy are facing the following:
- They recognize that the way code is written has changed vastly to include open source code and externally developed code that resides in multiple git repositories, distributed all over both inside and outside the enterprise.
- It is increasingly more difficult to monitor and track who has access to your code, where it resides and whether it has been cloned somewhere.
- As underlying infrastructure gets virtualized, it’s configuration is represented in code as well, making infrastructure vulnerable to code related attacks.
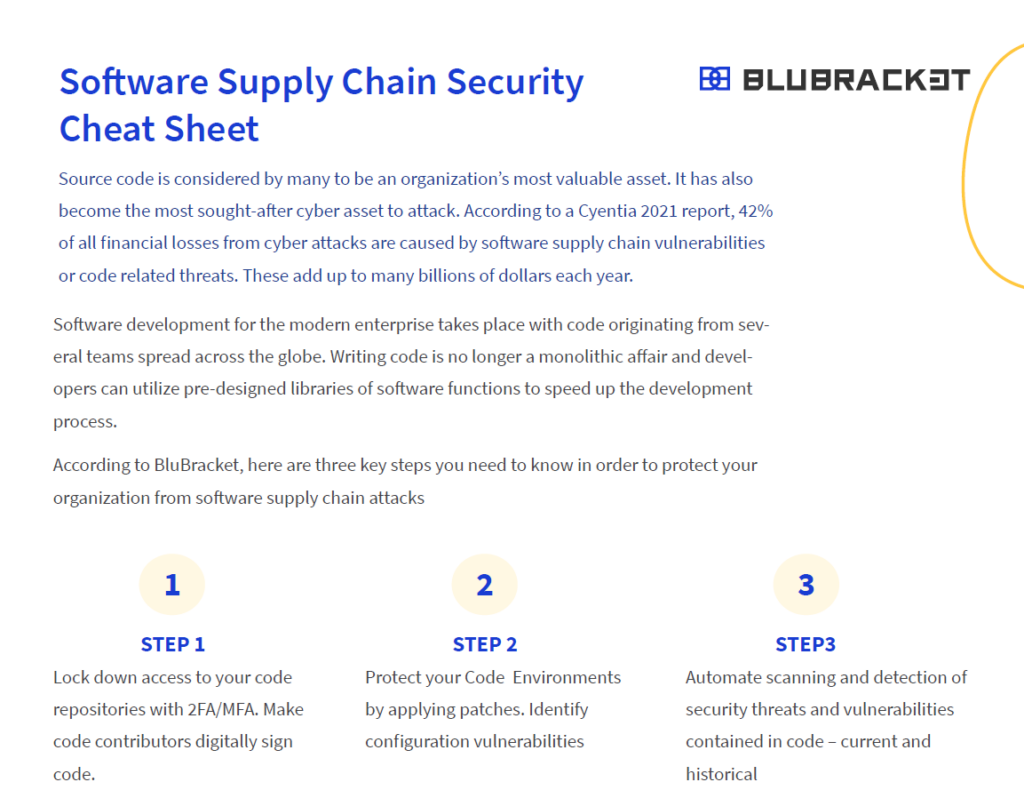
We have prepared a convenient software supply chain security cheat sheet (available for download below) for developers and security practitioners alike to quickly take steps to secure their software supply chain. Recommended steps include:
- Restricting access to code repositories with two-factor authentication (2FA)
- Securing developer / code environments with updated configuration
- Automate scanning for security threats and vulnerabilities in code in internal and external repositories and take steps to mitigate those
Security and DevOps experts both agree that keeping application security from slowing down CI/CD pipelines requires security to be integrated into all steps of the DevOps process. This has given rise to the discipline of DevSecOps, where security gets built-in and ideally provides a bridge between the other two functions.
Generally accepted application security solutions like SAST, DAST, and even open-source tools provide point protection, however, they do not close all the security gaps. Additionally, open-source tools can generate a very large number of alerts that include false positives as well. This can make it virtually impossible to remediate.
Key to providing developers more power and control over making sure that their code remains secure is adopting state-of-the-art risk-based application security solutions that can scan large volumes of code in repositories that will include not just the latest version, but the entire code history.
For more information on how BluBracket can help secure your code environment, please visit BluBracket.com.